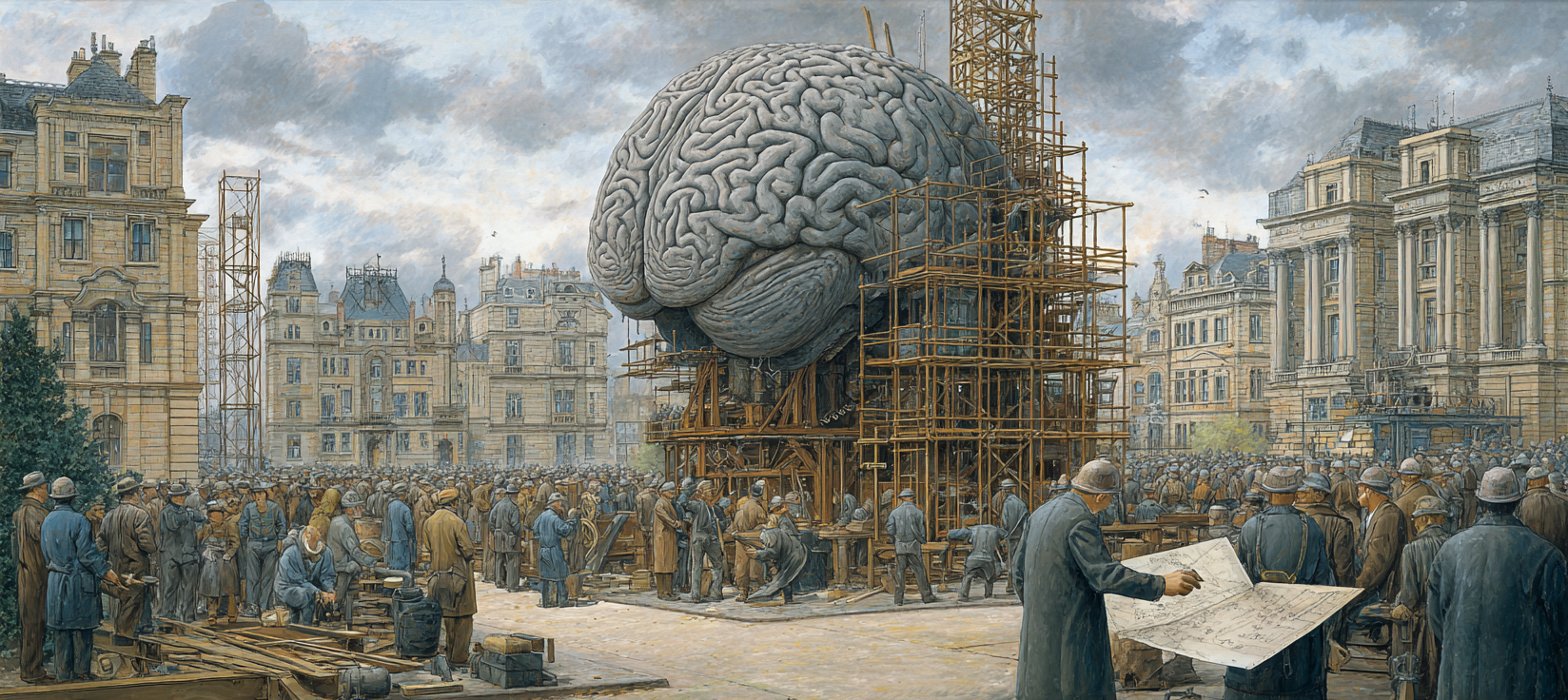
AI Part 7: LLM and Agent Security
Prior to the '90s, the world's telephone network ran on a collection of systems which implemented some variant of a protocol called MF Signaling (MF), as well as a formal version called System Signaling No. 5 (SS5).
The system was controlled by a series of tones. If you played those tones into a phone handset, you could obtain a certain measure of control over the phone network. Most notably, this was widely abused to make free long-distance calls.
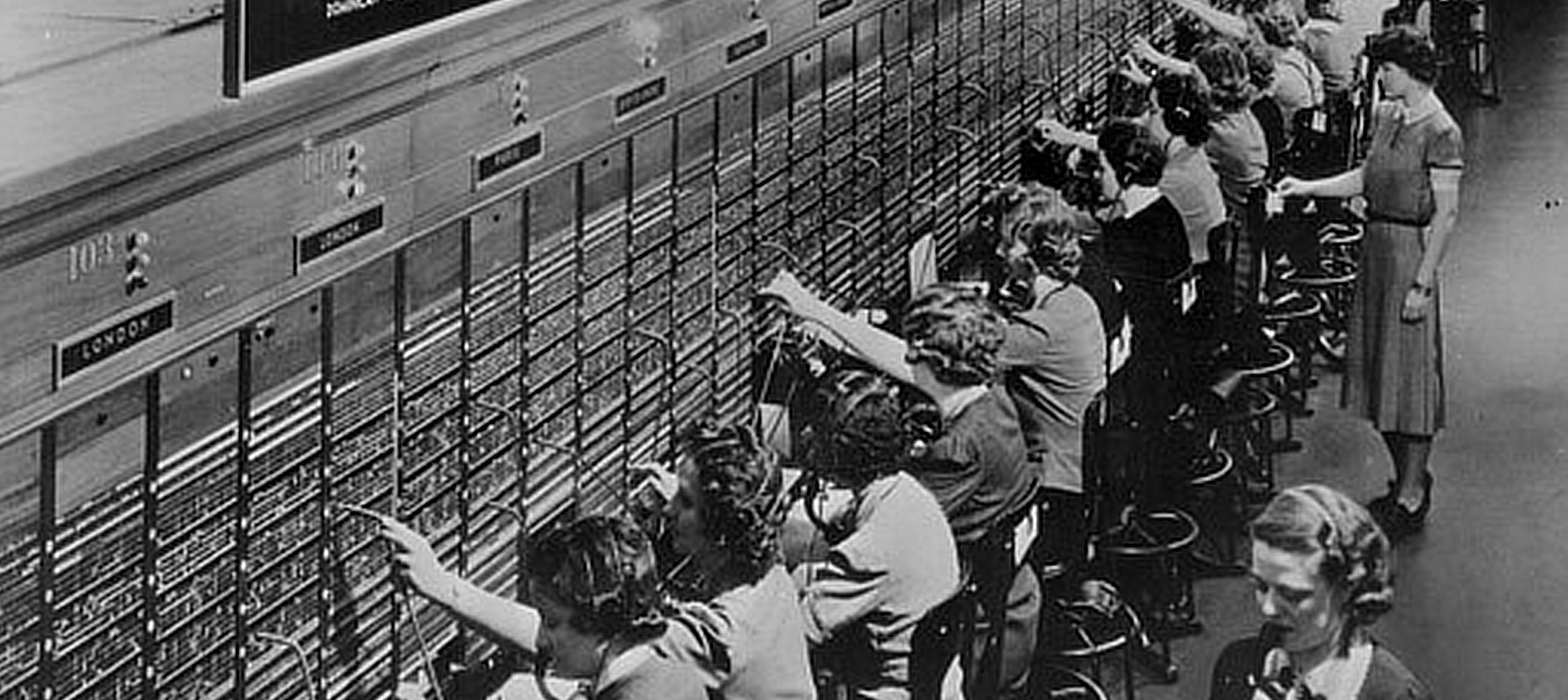
This worked because of the fundamental design of the network. In the old days, you picked up the phone, a human operator answered, you told them who you wanted to call, and finally they plugged a physical cable into a switchboard which effectively created one long wire between you and the person you were calling.
That idea of basically creating very long wires from individual segments was called circuit switching.
MF was designed to automate away the human operators, but a caller still needed a way to tell the automated network who they wanted to call. In the early days that was rotary dialing, but crucially the only way to send those signals was on the same pair of wires that were used to conduct the call. This is known as in-band signaling. At that time, the design was unavoidable.
The problem for the phone network is that it is impossible in such a system to know who is sending a tone. There is no way to differentiate if a tone was being introduced by the system, a legitimate operator, or a phreaker, as abusers of the system were known. They used a small device to create the necessary tones which was called a "blue box".
As a brief aside, a famous phreaker, "Captain Crunch", was so named because he found a whistle in a box of Cap'n Crunch cereal which just happened to perfectly produce the "trunk seizure" tone. Steve Wozniak and Steve Jobs were friends of Captain Crunch and built blue boxes for sale before starting Apple; a venture they abandoned after being robbed at gunpoint.